What is a “Kill Chain”
For this answer, you must fill in the blank!: The **********
military
What is “Threat Modeling”
What is the technical term for a piece of software or hardware in IT (Information Technology?)
asset
Introducing the Unified Kill Chain
In what year was the Unified Kill Chain framework released?
2017
According to the Unified Kill Chain, how many phases are there to an attack?
18
What is the name of the attack phase where an attacker employs techniques to evade detection?
Defense Evasion
What is the name of the attack phase where an attacker employs techniques to remove data from a network?
Exfiltration
What is the name of the attack phase where an attacker achieves their objectives?
Objectives
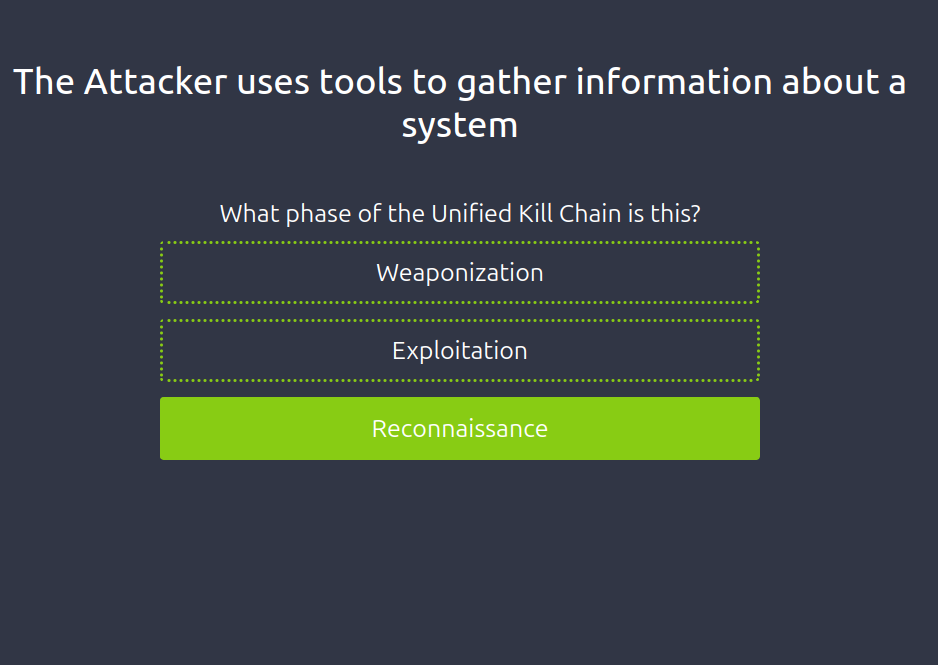
Phase: In (Initial Foothold)
What is an example of a tactic to gain a foothold using emails?
Phishing
Impersonating an employee to request a password reset is a form of what?
Social Engineering
An adversary setting up the Command & Control server infrastructure is what phase of the Unified Kill Chain?
Weaponization
Exploiting a vulnerability present on a system is what phase of the Unified Kill Chain?
Exploitation
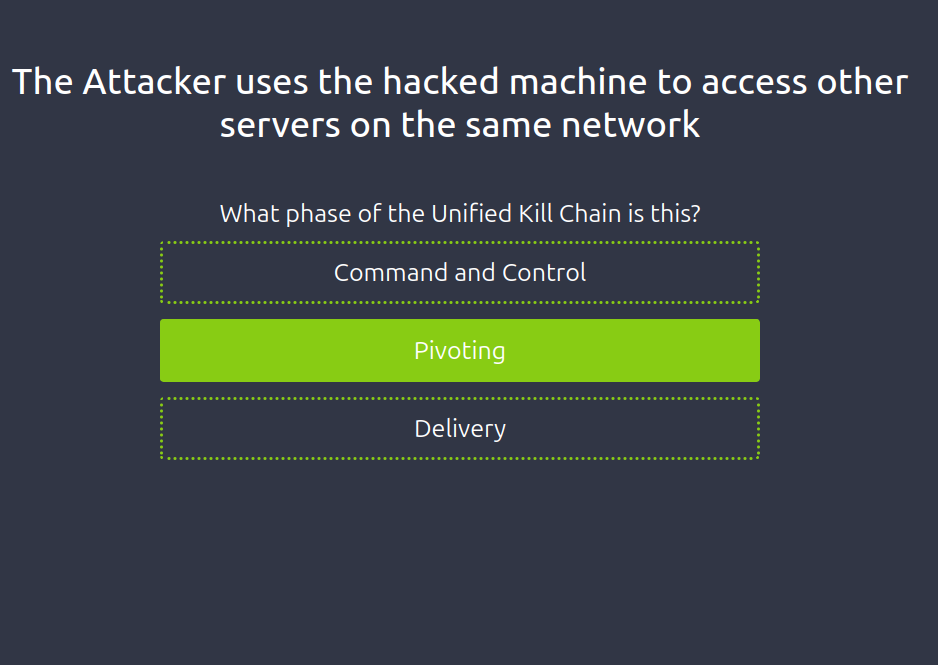
Moving from one system to another is an example of?
Pivoting
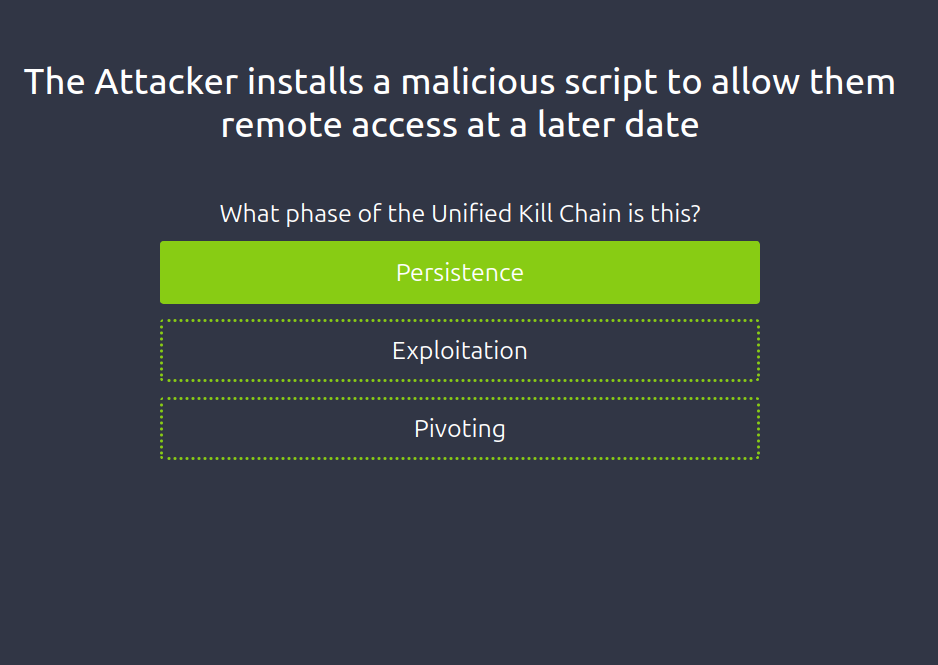
Leaving behind a malicious service that allows the adversary to log back into the target is what?\
Persistence
Phase: Through (Network Propagation)
As a SOC analyst, you pick up numerous alerts pointing to failed login attempts from an administrator account. What stage of the kill chain would an attacker be seeking to achieve?
Privilege Escalation
Mimikatz, a known attack tool, was detected running on the IT Manager’s computer. What is the mission of the tool?
Credential dumping
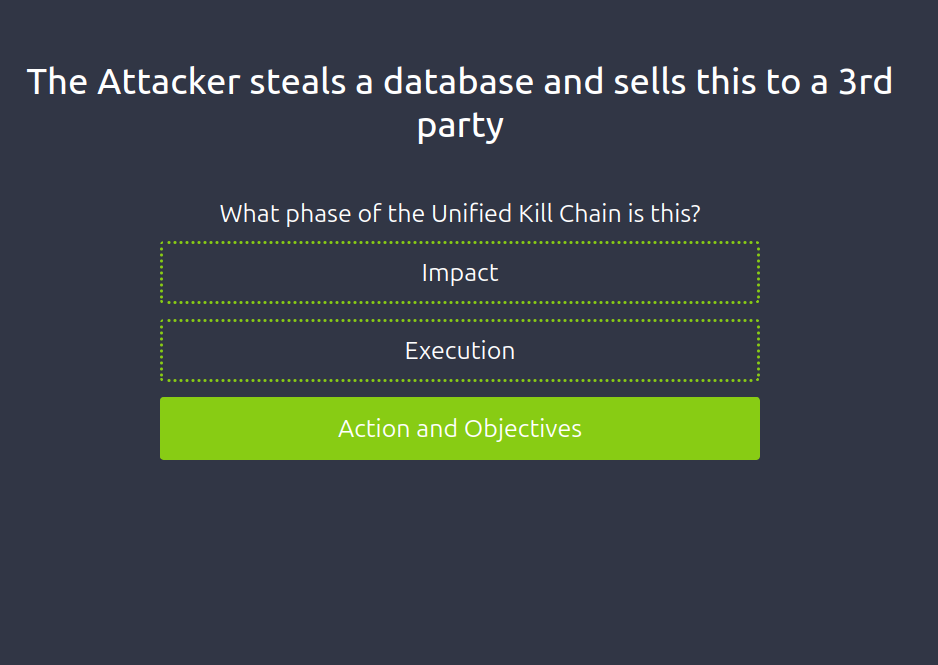
Phase: Out (Action on Objectives)
While monitoring the network as a SOC analyst, you realise that there is a spike in the network activity, and all the traffic is outbound to an unknown IP address. What stage could describe this activity?
Exfiltration
Personally identifiable information (PII) has been released to the public by an adversary, and your organisation is facing scrutiny for the breach. What part of the CIA triad would be affected by this action?
Confidentiality
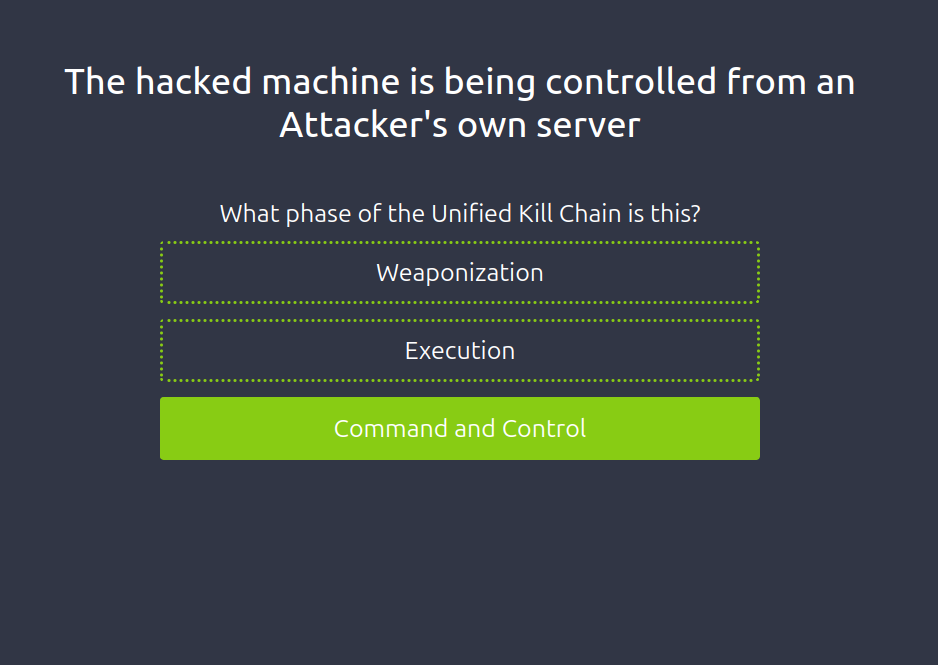
Practical
Match the scenario prompt to the correct phase of the Unified Kill Chain to reveal the flag at the end. What is the flag?
- `THM{UKC_SCENARIO}
- 3`
.png)